Introduction
Last year I participated in Asis CTF Finals and I was pretty interested in a 0 solve hardware challenge - e-cart. Today, I’m going to show you my solve and how easy it actually was after you figure out the beginning.
Description
We have a file associated with an e-cart that contains the key to the flag. Once you find the flag, ensure that you accurately fulfill all the requirements specified within it.
Solve
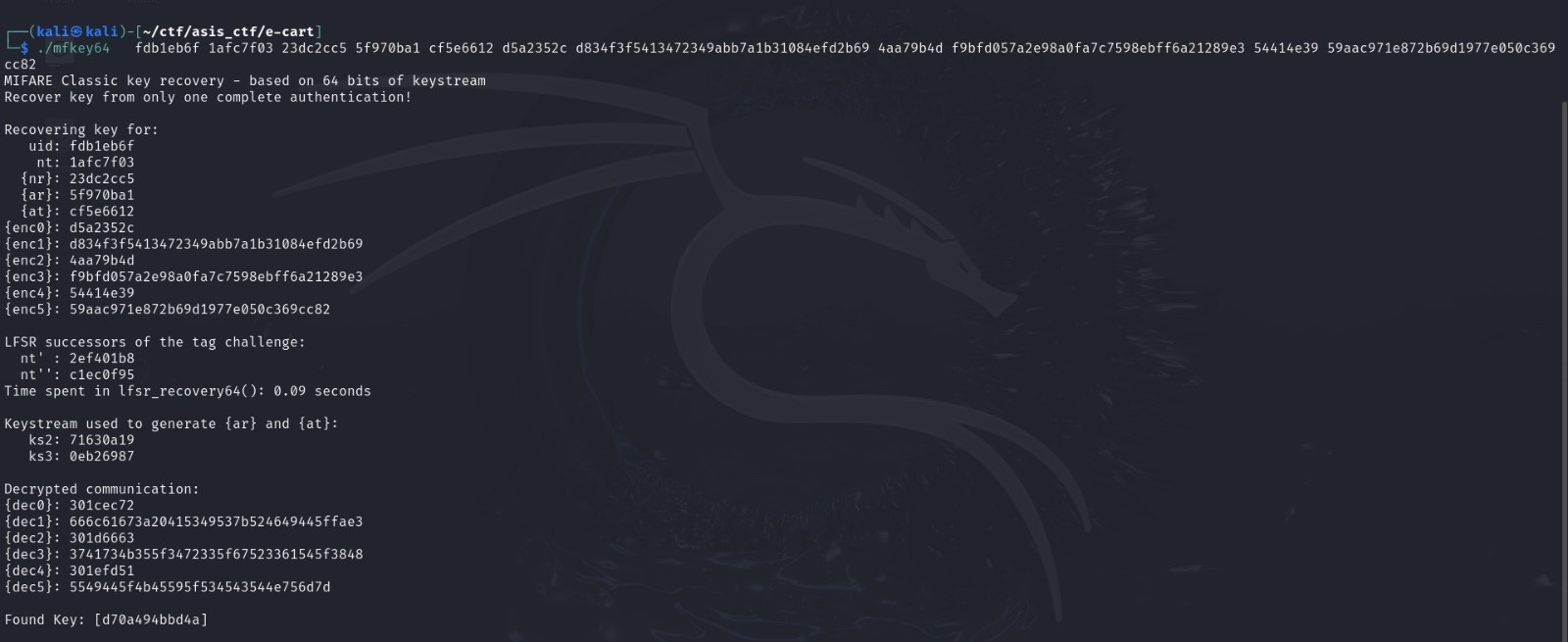
First of all, you had to figure out that this is a trace file for a Mifare Classic nfc card and from there navigate your way to decrypting the communication. Fortunately, there is a tool mfkey64 which does just that. Make sure to retrieve the card uid, nt, nr, at and ar fields (think of those as the values used to establish the handshake) in order to be able to decrypt the communication.
Use proxmark3 in order to analyse the trace file and retrieve the specified fields.
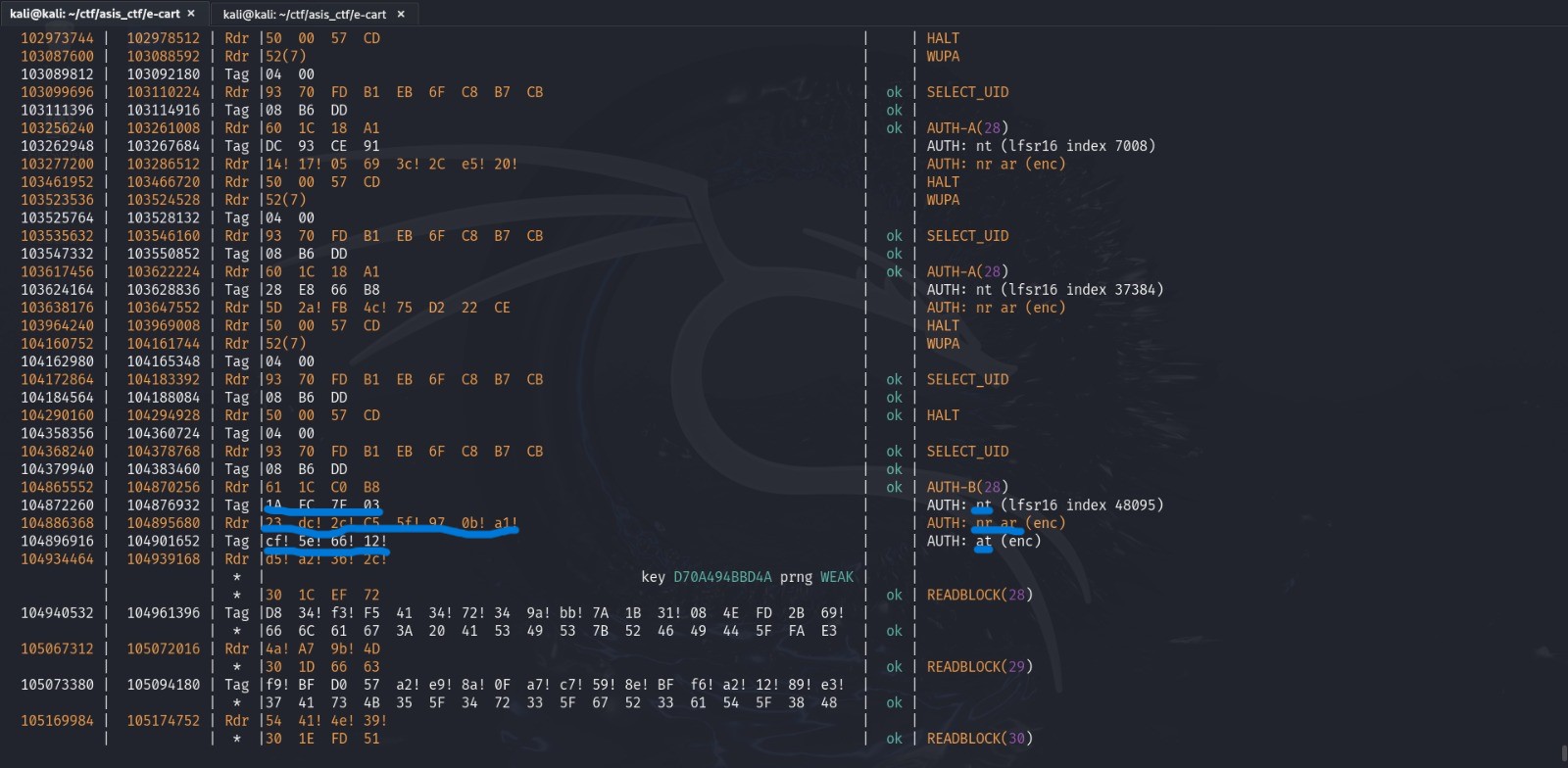
After spinning up proxmark3, load up the trace file and run trace list -1 -t mf to specify the type of nfc card that the trace belongs to. We’re going to be greeted with some long output, but only the last part counts.
After extracting those, we paste those into the tool alongside the encrypted blocks, which are just below the fields.
Finally, with the decrypted communication we just paste this into cyberchef to decrypt the hex data and we got ourselves the flag.